Checking a bank balance, shopping on Amazon or downloading a new app are things we all do online nearly every day. But is using the internet safe? As the digital world drives more of these daily tasks, cybercriminals are becoming more sophisticated and finding unique ways to access your data and identity, making internet safety more important than ever.
The internet can be used to stay safe, but there are also cybercrime risks. Cybercrime is any criminal activity carried out online that can happen to anyone. Cybercrime is only becoming more prevalent. In fact, a study conducted by the University of Maryland about internet safety revealed that cybercrime is committed every 39 seconds in the U.S. It is also estimated that 1 in 3 Americans are affected by cyber-attacks yearly.

Internet safety: Main takeaways
Scammers can access your computer and personal information through a variety of methods. Online scams can take the form of fraudulent emails, bogus online ads, compromised websites, false job applications or downloading infected files, as just several examples. If you’re wondering how to stay safe online, always be wary and only interact with trusted sources. Below are some further online safety tips.
Tips for staying safe online
Below are some tips to help avoid online risks. You can also look at our guide on how to keep kids safe online and our guide on internet basics for seniors.
- Avoid giving away personal information, such as if a website demands your phone number. Avoid listing very personal data like social security numbers. Either don’t share your email, or create a throwaway email.
- Make sure your passwords are secure. Long, complex passwords with special characters, lowercase and uppercase letters and numbers are harder to hack. You might consider using a password manager to ensure your passwords are saved and auto-entered.
- Keep website safety in mind by only visiting secure websites. Visit trusted websites and avoid unknown and dubious-looking ones. Only make purchases through secure sites. If it says “https” instead of “http” it means the site has been secured using an SSL Certificate (S stands for secure). You may see a lock before the URL in your browser indicating an https address.
- Have solid privacy settings on any online accounts such as social media. You might consider turning off location tracking on any apps you use. You might also set up a VPN, or virtual private network, to use for browsing the internet. A VPN can help increase internet browsing safety by hiding your data from hackers. Also, watch out for signs of hacked Wi-Fi and ways to secure your router.
- Be wary of any emails you open and links you click on. Only click on trusted links, if you click them at all. Keep an eye out for phishing, too. You should never have to provide sensitive data over email, especially social security numbers or banking information.
- If you’re unsure if a website, text or email looks suspicious, talk to a trusted family member or friend for their opinion. Reviewing information with others is especially important if a contact’s email has been spoofed and that dubious information is seemingly coming from that contact.
What risks should I look out for
There are several main online risks to safety on the internet. While not an exhaustive list of threats to E-safety, it’s important to watch out for phishing, hackers gaining access to your network or computer, malware, ransomware and data leakage.

Phishing, scams and frauds
The main issues to watch for during everyday internet use are phishing, scams and frauds.
What is phishing?
Phishing is when a hacker poses as a trustworthy source in order to gain access to your sensitive information. Phishing is considered one of the top 5 cybercrime types, along with tech support, extortion, non-Payment/non-delivery and personal data breaches. It’s the cybercrime that has accumulated the most victim loss in the past 3 years.
The lure is most often a familiar-looking email, website or ad and the trap is requesting personal information, such as your bank account information, Social Security number, password, etc.
What is a scam?
A scam is any scheme that takes money from an unsuspecting person.
Scams can take various forms, but there are five most popular ones. A scammer may pose as a lottery, sweepstakes or competition. They say you won, but then you must pay taxes or fees upfront to receive your non-existent winnings. Scammers may also create fake dating profiles, lure someone into a false relationship, and ask for money.
Sometimes, you may see a scammer posing as your bank to request banking information. Scammers may also pose as a tax authority and say they need personal information or that you are behind on tax payments.
Finally, various COVID-19-related scams have cropped up, from offering false COVID-19 testing/vaccines to false funeral assistance to selling fake health insurance such as “corona insurance.”
What is fraud?
Fraud is the more general term that scams fall under. While scams always relate to money loss, fraud includes many types of deception.
Five main types of online fraud can threaten your internet safety. Advance fees or banking fraud require a fee for a false deal to process. Mail fraud is any fraud that happens through physical mail. Counterfeit health and beauty products are broad categories encompassing any product that makes false medical claims, such as a miracle weight loss supplement. Internet fraught is another broad term that means any fraud that happens online. And elder fraud covers any fraud that goes after an elderly person.

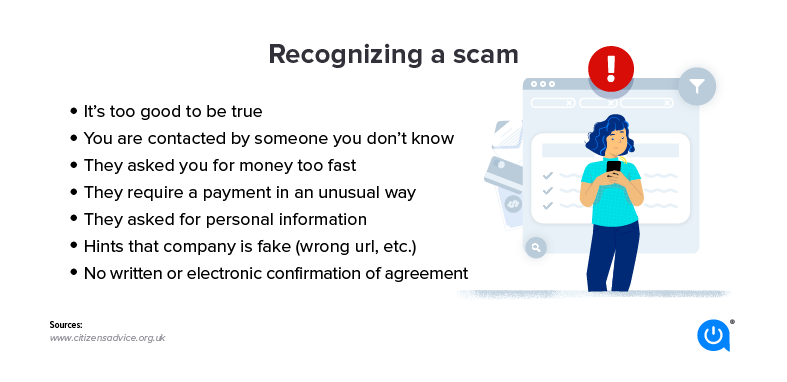
How to recognize cyber attacks and risks
Take your E-safety seriously by learning how to spot the signs of a cyberattack:
- Unsolicited or unexpected contact: If you receive an email or phone call that says you need to do something urgently but the message is completely out of the blue, this is likely a scam.
- Asks for personal information or money: If the content of the message you have received immediately asks for personal information, such as your Social Security number, that is a huge red flag. There is rarely a time a website or even your bank account will request personal information out of the blue. Similarly, don’t send money to unverified sources.
- The use of threatening, urgent language or ultimatums: Often, cybercriminals will use fear as a tactic to get you to comply and give up information. If you receive a cryptic message that contains threatening language, do not panic, it is likely just a phishing email.
- Amazing promises: If you receive a message with an offer that seems too good to be true, such as winning a million dollars, there is a high likelihood it’s a scam.
- Unexpected changes to your accounts or other information: If you notice any unexpected changes to your private accounts or see unfamiliar accounts on your credit report, you are likely a victim of fraud. You may also notice bills/statements stop coming via U.S. mail, get credit cards you never applied for, or notice changed passwords or other information.
- Spelling, punctuation or grammar errors: If you notice grammatical mistakes and spelling errors in the content of the message, the message is likely not from a reputable source. Trustworthy websites rarely send out emails, letters or ads with errors since they tend to be heavily proofread. You may also see incorrect URLs or domain names.
How to stay safe online
Wondering how to stay safe online? Reduce your risk by following online safety rules. Below are some online safety tips to make sure you don’t become a victim.
- Protect your computer with security software: Installing security software is a great way to keep your computer safe from viruses. Popular options include Bitdefender Antivirus Plus and Webroot SecureAnywhere for Mac.
- Encrypt your email: Encryption certificates like SSL.com provide can ensure your private info reaches the intended recipient without being intercepted. The email is transformed into unreadable text and the person on the other end will have the decryption key.
- Protect your accounts by using multi-factor authentication: A great way to ensure hackers do not access your private accounts is by using multi-factor authentication, such as Okta.
- Call banks and major companies to confirm personal information rather than email: Contacting your bank or any other company to discuss an email you received is a much safer option than responding to a phishy email directly.
- If using work-related technology, educate coworkers and staff: Immediately let your company know if you have accidentally fallen victim to fraud. Additionally, make sure your coworkers and staff are aware that you are being targeted for scams so they can be on the lookout for them as well.
- Watch what you share on social media: Do not post photos that reveal personal information. Do not post your vaccination card, driver’s license, credit card, etc.
- Consider using “incognito mode” for browsing: One extra precaution you can take to prevent having your activity and data tracked is by using incognito mode on your computer. This is not a fool-proof option but it will provide you with some additional security.
- When picking your ISP, check out their available security measures: Many ISPs will offer free security features with some or all of their internet plans. Consider this factor when choosing your ISP.

Tips to recognize scams via email
- Check the sender: Do you recognize the sender? If not, be careful with the content of the email.
- Hover over links before clicking on them: Does the URL match the description in the email? If not, do not click.
- Think: Hackers use urgency to draw people in. Ask yourself if the request makes sense. Look out for words like “Urgent!” and “Click now!”. Other phrases like “log in here” or “manage my preferences” are often employed to trick you into clicking on malicious links. And never click on “Unsubscribe” in spam, just report it as junk.
- Look: Check if there are errors in the body of the email/sending address or it doesn’t look like a usual email that you receive. Micortofs is not the same as Microsoft.
- Avoid: Do not use your work email address for personal accounts (this includes such things as LinkedIn, Spotify, and any other account that is not work-specific). This will reduce the number of personal emails you receive on your work account and help protect you from accidentally clicking a link in an email designed to look like it’s from one of those accounts.
Internet safety protocols
- Your state consumer protection office: Your state consumer protection office can help you if you have lost money or possessions due to a scam. You can find your state’s office here.
- The Federal Trade Commission: The FTC is your best bet if you have fallen victim to identity theft. They will create an individualized recovery plan and help you complete the required forms to manage your situation.
- Internet Crime Complaint Center: If you would like to report an internet crime, the Internet Crime Complaint Center through the Federal Bureau of Investigation is the way to go.
- Econsumer.gov: Econsumer.gov is a great resource for reporting international scams and learning how to avoid scams in the future.
- IRS: Contact the International Revenue Services (IRS) for any issues relating to tax fraud.
- Anti-Phishing Working Group: To help stop the spread of phishing emails, you can report any fraudulent email you have received to the Anti-Phishing Working Group.
- SCAM (7726): If you receive phishing messages over text, also known as Smishing, forward those messages to SCAM (7726) to help stop the spread.
FAQs
Wondering about internet safety? It’s a general term that refers to practices that keep you protected online. You might employ tactics like having strong passwords, using a VPN, being wary of unknown contacts, staying up to date on current scams going around, not giving away sensitive data and not sending money.
Yes, if the website is not secure or you willingly give information. Scammers can pose as your bank, a tax authority, a seller or anything else they choose to attempt extracting money or data. This is why internet browsing safety and website safety are such important issues.
Even if you’re concerned about safety on the internet, you can still provide information online, as long as you know the site is secure and reputable. Some websites use name and address information to ship things or verify your identity. Check that the site has https in the URL and/or a lock in front of the URL.
One of the top online safety rules is that very sensitive information should rarely if ever go online, such as social security numbers. If you find you must list this information, such as if you’re working with a digital bank, make absolutely certain the company is legitimate and the website is secure. Search reliable consumer reports and scam alerts to find out about the online service you are thinking of using. Check with the Better Business Bureau, FBI scam alerts or FTC scam reports.
Allconnect: Let us compare providers for you
Why should you choose Allconnect? We’re the #1 broadband marketplace in the U.S, meaning you can trust us to search, compare and order internet and TV service for your home.
Get started
Written by:
Michelle Honeyager
Michelle Honeyager is a contributor for the Allconnect team. She has been writing professionally for over 10 years, and covers topics pertaining to home internet tech and internet service. She graduated from Mou…
Read more
Edited by:
Robin LaytonEditor, Broadband Content
-
Featured
![How hackable are the smart devices in your home? We reveal the most vulnerable rooms]() How hackable are the smart devices in your home? We reveal the most vulnerable rooms Lisa Iscrupe — 9 min read
How hackable are the smart devices in your home? We reveal the most vulnerable rooms Lisa Iscrupe — 9 min read -
Featured
![Is public Wi-Fi safe? No, but it is necessary]() Is public Wi-Fi safe? No, but it is necessary Camryn Smith — 5 min read
Is public Wi-Fi safe? No, but it is necessary Camryn Smith — 5 min read -
Featured
![10 questions you should ask before choosing an internet service]() 10 questions you should ask before choosing an internet service Ari Howard — 7 min read
10 questions you should ask before choosing an internet service Ari Howard — 7 min read
Latest
-
Thursday, July 25, 2024
Worried about losing your signal? This is how to keep your satellite dish cleanDavid Anders — 6 min read
-
Tuesday, July 23, 2024
The best free TV and movie streaming services 2024Camryn Smith — 5 min read
-
Tuesday, July 23, 2024
Everything you need to know about internet speedsRobin Layton — 8 min read





